One of the most talked about cryptocurrencies in recent months is Trezor Model T. It’s a USB-powered device that boasts a new biometric authentication system that offers users an unprecedented level of security. With all this talk, it can be hard to keep up with everything that’s going on, especially with so much hype around cryptocurrency in general. Recently, a security researcher known as “The Grugq” published a paper detailing how he was able to bypass two-factor authentication (2FA) on the Trezor Model T cryptocurrency hardware wallet.
What is the Trezor Model T?

The Trezor Model T is a hardware wallet that was created by SatoshiLabs. It is a secure device that can be used to store bitcoins, ether, and other cryptocurrencies. If you ever debate Trezor One vs Model T, keep in mind that the T model has a number of features that make it an attractive option for those looking to keep their cryptocurrencies safe.
One of the benefits of using this crypto wallet is that it is capable of generating two-factor authentication codes. This means that even if someone were to gain access to your device, they would not be able to access your cryptocurrency holdings unless they also had the second-factor code.
Another feature that makes the Trezor Model T stand out is its ability to store multiple currencies. This means that you can store bitcoins, ether, and other cryptocurrencies on one device without having to worry about them being lost or stolen.
Overall, this is a popular choice among cryptocurrency investors due to its security features and ability to store multiple currencies.
How to use it?
If you’re looking for a hardware wallet that’s as secure as it is user-friendly, the Trezor Model T may be what you’re looking for. This hardware wallet is easy to use and has an intuitive touchscreen interface, making it a great choice for anyone new to cryptocurrency.
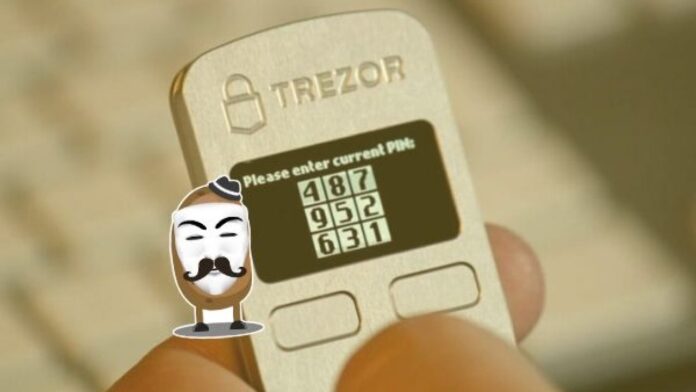
To set up your Trezor Model T, first, make sure you have an internet connection and install the free Trezor Wallet software. Once installed, open the app and click on “New Wallet.” Next, enter your 12-word backup phrase and click “Next.” You’ll then need to set up two additional security measures: a pin code (to protect your wallet from unauthorized access) and a passphrase (to protect your wallet from being hacked). To create your pin code, type in your 24-character long pin code into the text box and click “Create.” To create your passphrase, start by selecting a word or phrase that is at least 8 characters long. Make sure you remember this password because you’ll need to enter it each time you start your Trezor Model T. Finally, click on “Next” to finish setting up your wallet.
Now that your Trezor Model T is ready to use, all you need to do is store some cryptocurrencies inside of it. To do this, first select one or more cryptocurrencies you would like to store inside of your Trezor Model T. Next, open the Trezor Wallet app and click on
The vulnerabilities of the Trezor Model T

It is marketed as being resistant to hacking and theft. However, recent research has shown that the Trezor Model T can be hacked.
The first vulnerability of the Trezor Model T involves its use of seed words. The seed words are required to initialize the wallet and are 12 random words chosen by the user. These words are not encrypted and can be accessed by anyone who knows them. Due to this, it is possible for attackers to access funds stored in the Trezor Model T if they know these seed words.
The second vulnerability of the Trezor Model T relates to its security PIN code. The security PIN code is used to protect against unauthorized access to your wallet. However, it is possible for attackers to guess or steal this code if they know enough information about you, such as your name and address. If an attacker has access to your wallet with your security PIN code, they can withdraw all of your funds without requiring any additional authentication procedures.
Both of these vulnerabilities have been demonstrated in practice by researchers from Sicurezza Informatica and KU Leuven University. They were able to access funds stored on a TREZOR device using only knowledge of the user’s name and address. By guessing or stealing the security PIN code, they were also able to withdraw all of the user’s funds.
Given these vulnerabilities, it is important that users always keep their seed words and security PIN code safe. They should also use a different password for each of their accounts, and never keep these passwords in the same place where they store other sensitive information.
How can you protect your Trezor Model T?

1) Always keep your TrezorModelT plugged into a power outlet when not in use. This will ensure that if it is hacked, the hacker won’t be able to steal any of your cryptocurrencies.
2) Always use a strong password Make sure that it is at least 8 characters long and includes at least two different types of characters (e.g., alphanumeric, special symbols).
3) Never leave your Trezor Model T unattended or unprotected. If you do, make sure to take precautions such as encrypting your wallet with a passphrase before leaving it unattended.
4) Never give anyone access to your crypto wallet except for those who you trust absolutely. If you ever have to hand it over to someone else, make sure you securely encrypt the device beforehand so that they cannot access any of your cryptocurrencies.
Conclusion
Yes, the Trezor Model T can be hacked. In fact, there are many different ways to hack a Trezor Model T and access your cryptocurrencies. However, the best way to protect yourself is by using a strong password and by never trusting anyone who asks you for your Trezor private key. If you do experience a security breach, we recommend notifying Spenden immediately so that they can provide support in mitigating any damage.